Late in 2016 I was honored to deliver a keynote at
Hamburgsides, a neat'n'boutique side event of CCC. The talk was titled
'The Magic Superpowers of a well-established "Us"'. Naturally, it was all sparkly fairies and we are hackers expect us hugging the community fuss. Not ;)
A well-established "us" is a team or a group of people who stick together and work together no matter what, who have recognized a shared goal and support one another on the way there. The "us" I have seen on plenty of occasions, it helps CTFers capturing their Fs, it helps incident responders in staying awake for 48 hours, it gets projects done cheaper err quicker I mean, than what the plan was. It is magic.
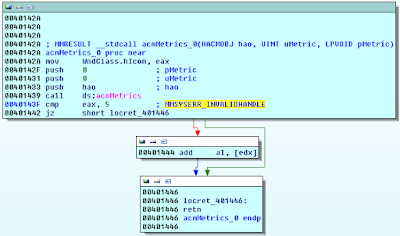
Last year in November I have witnessed an "us" I had not been aware was there. Indirect base of the Hamburgsides talk is a workshop I organized two years in a row, an event named BlackHoodie. It's a women-only reverse engineering bootcamp, aimed at female engineers who are interested in low-level tech but who are hesitant to jump right at it on their own. The first edition was held at University of Applied Sciences St.Pölten, and in 2016 it was again a 2-day event, this time located at the G Data offices in Bochum, Germany. Believe it or not, 27 attendees made their way, we were 14 nationalities from 5 different continents, with backgrounds in computer science, data science, mathematics, history, applied physics, and, hold your breath, astro physics. We did static RE on an IRCBot, discussed packers and went through some of Upatre's anti-analysis tricks with a debugger.
Under the line, the project is nothing more than two days sitting together talking about a binary. In reality though it is much more. I have failed repeatedly in understanding why the guerrilla-women-RE-bootcamp concept was thus far so successful.
Now, how do I measure success? The magic "us" is a start, but also just a start. The past few years I've been talking so much about women-in-technology, and received many titles for it too; being an advocate and a role model. That’s for some part an honor, for another though, one grows quite tired of being randomly reminded of being -the girl-. But what to do about it – more talking?! Certainly not.
A month ago I went to Troopers conference in Heidelberg, and ran into my workshop homies, four of them. That wasn't planned, just happened. One of them did a remarkable keynote, two presented their security research. Over the past year I saw BlackHoodies at conferences, read papers and blogposts written by them, connected researcherettes over research topics, asked them questions and answered theirs. And that was when I realized, so this is where we are, the workshop is being successful.
XYZ-Only Concepts
Twice a year I do a class of malware reverse engineering at University of Applied Sciencs St. Pölten. It is usually a men-only class. Like with so many of the CTFs, the conference call for papers, the security challenges, the coding challenges, the workshops paid and free, few women dare to sign up. Of course, potential answers for why this is so could fill a book; personally though I believe a major point is that many just don’t feel like they’re supposed to.
I've had a number of controversial conversations, on whether secluding a minority in order to support it makes sense or not. To be honest, I am not 100% sure myself, whether a women-only or given-minority-only approach is in sole favour of said group. There is plenty of arguments which make me assume so - I understand the event as a safe and inviting space, for the present participants to be an inclusive and supportive environment. Countering arguments, are concerns the participants might appear weak or preferred, for receiving protection and special treatment. But what I mean to do by creating space is not building walls; it is just that, creating space. Also I'd like to counter, the workshop is not a tea party, we’re actually working hard, trainer and attendees alike. I make sure everyone is suffering, I promise. Finally, the topics discussed aren't exactly top secret;
twinker-twinker ;)
I hope, that with a special invite I can appeal to the very group I want to strengthen, and make them understand that we're having fun; as in, come to the dark side, we got cookies. It is really about evening out opportunities. Equal opportunities mean, that everyone has the same start from the very beginning, which is too often not the case. Because, if you don't feel as comfortable as the person next to you, it is not an equal spot to be in.
Finally, yes, we came to smash patriarchy; except that we didn't. It isn't and has never been an us-against-the-world approach. We sit together and practise, then do amazing things, with confidence. Imagine this like a late-90s garage punk band. No one with dignity ever told THESE to stop, did they.
The Otherness
I asked the (hoodie-dressed) Hamburgsides audience, imagine, you, being the daring hacker that you are, if you were to start work at a real estate agency tomorrow, and had a meeting scheduled with property tycoons, wearing a suit and talking finance, how confident would you feel going in there?

I truly believe so, comfort is a factor. Feeling like belonging somewhere, being accepted, welcomed, having your homies around, that’s what gets humans to engage, speak up and if necessary, fight. Wrestling down the otherness, if one is just bound to stick out, is a thing, and mind you, it is not only about gender. Otherness in tech is not at all a problem of women, not even primarily. I've seen boys who are scared too, plenty of them, then I watched them learn stuff, build confidence, be someone and own their topic. On the way though, they need the very same kind of support. Buddies, role models to measure their own growth, constructive feedback, appreciation for success. In lots of my students, I can see a near-desperate desire to rule a topic, any topic, for exactly these reasons.
While it looks a lot like being a woman at BlackHoodie matters, in reality it is about creating a place where for once it doesn't matter. Not being the alien for once is nice, and makes feeling daring so much easier.
Being Padawan
The security field by itself is very competitive. The whole idea of hacking is a lot about confidence and courage, it is key to walk into the unknown and to then tap in the dark for a considerable amount of time, not giving up. This is a rather toxic prospect for a community that classically lacks self-esteem and ever so often suffers imposter syndrome. I’ve met but so many smarts and smartettes who were very quick in saying "I will never", or who would just not be happy upon hearing '"you're doing great", from me or anyone else. I've literally urged someone to grow a fake-it-til-you-make-it attitude, faking being able to do something she was already good at, just so she'd get over the confidence building a little quicker. I am that evil.
I think there might be solutions to this though, other than tricking the candidates. Our industry, believe it or not, is full of Master Yodas. Skilled individuals, who are happy to offer a helping hand to worthy Padawans, give advice, share experience and push the procrastinators.
But then, how to live up to the Padawan-ing? I'll tell you about my own secret force, what it is that gets me to not analyze malware but to rip it apart, to not write write-ups but testimonies, frequently fat enough so the printout can literally be used in hit-back attacks. It is not curiosity, neither is it nice salaries or, I'll admit, the drive to make the world a better place. I've identified my motivators as anger and fear; anger, that some wouldn't believe that I was able to do what I wanted to do, and fear that I would disappoint others who trusted I was.

A friend once told me that passion wears off, while greed is sustainable. I also think that’s funny, but I personally believe that my greed is limited, while my fear is not. Needless to say, this concept is far from perfect, but it taught me over time what it takes to become a worthy Padawan. It means to pick the challenging and scary tasks, to do things that are too difficult; then sticking to it, making it yours. It means practise, practise and practise more. Stay hungry, stay humble. And in the end, never forget to trust Yoda. A great Yoda told me a short eternity ago that reverse engineering is one part being smart, three parts being able to bear pain. So there's that. Days of failing to eat, sleep and shower, because the assembly in front of you hasn't given up yet.
Building a Community
Frequently individuals come up and ask me how to support the effort. Yes, indeed, plenty of fellow-hackers would be happy to welcome plentiful fellow-hackerettes. So, I came to think, landslides don't change things for the better, but little actions do. Can't really regulate people into happiness, can we? This is why I put together a list of things that help getting more smart imposters into security; and a list of things that are rather in the way.
How to support:
- give them a smile, be welcoming
- ask questions about their work, and listen
- engage in conversations
- before you explain things, make sure the explanation is needed
- help folks understand their own achievements
- push, gently, then support
- connect other like-minded minds
- naturally, be a decent human being at all times
On the other side, don’'t ...
- ask how did you get here, what are you doing here, why did you decide to do $technology
- ask for a phone number, a date or a place to spend the night
- assume from the start someone is present because of their significant other
- assume from the start a third party is responsible for someone’s achievements
- take over someone else’s tasks
- intentionally play down someone’s achievements
- act offensive
It's really not easy to see the world through the eyes of someone else. I've explained to curious questioners so damn often why I decided to work with binaries, that I got to think myself I'm a weirdo. Just sayin.
There lies great potential, right there at the feet of the smart but scared infosec population. Potential, that security teams also desperately need. I have never been in a position where I was responsible for other people's work, can understand though, how such team dynamics turn out complex in practise. If you build a team, of course skill is key, but there is a lot more to it. You'll want people on your team who appreciate feedback, who are hungry. You want the learners, not the know-it-alls, you want the smart folks that manage problems for you, not those who need to be managed themselves. A good friend of mine told me this, in a hotel bar in Vegas - I hire specialists to have them tell me what to do, not the other way around. You'll make your employees specialists by handing them the difficult tasks, not the simple ones.
In a recently published
blog post Justine Bone points out how "... we as minorities are not a problem, but an opportunity, and we'd probably find the whole scene more appealing if it were addressed as such". True that. I'm all in for showing what an amazing opportunity we are.
The next BlackHoodie is being planned, will take place this fall or winter, probably in Europe, but that is still to be decided. It will always be free, it will always be hardcore. Lookin forward \m/
Slides for the Hamburgsides keynote can be found
here and the recordings of
this talk and other Hamburgsides sessions can be viewed
here.